For over two decades, the Open Worldwide Application Security Project (OWASP) Top 10 has served as a central reference and common language for developers, security professionals, and technical leaders.
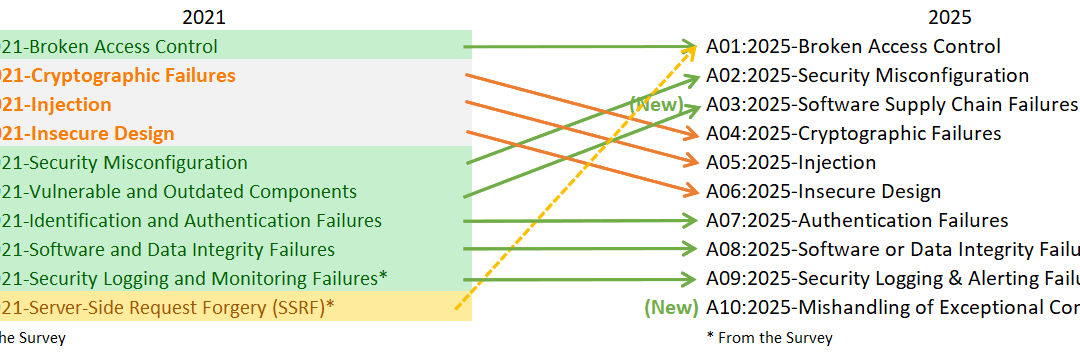
The newly released 2025 edition signals a fundamental shift in application security: the focus is moving away from isolated coding errors and toward systemic, architectural flaws in how applications are built, configured, and operated.
The Big Debuts: Two New Categories
The 2025 list introduces two major categories that reflect the growing complexity of modern software systems.
1. Software Supply Chain Failures (A03)
This is arguably the most significant change. Replacing and vastly expanding upon the 2021 “Vulnerable and Outdated Components” category, A03 encompasses the entire software supply chain.
-
Beyond Libraries: It covers third-party dependencies, CI/CD pipelines, package management, and trust in external vendors.
-
The Impact: Supply chain attacks have proven to be highly scalable, effectively bypassing traditional security controls by compromising code before it ever reaches production. Despite having fewer occurrences in testing data, supply chain vulnerabilities yield the highest average exploit and impact scores.
2. Mishandling of Exceptional Conditions (A10)
This entirely new category focuses on how systems respond to abnormal, unpredictable situations.
-
The Risk: When applications end up in states they weren’t designed to handle, it can lead to exposed stack traces, unhandled exceptions, or worse—systems failing “open” instead of “secure.”
-
Propagation: In distributed architectures and API-heavy environments, a mishandled error in one service can rapidly propagate to others.
Key Mergers and Movers
The structure of the list has also been rearranged to reflect how real-world attacks are carried out today.
-
Security Misconfiguration Surges to #2: Jumping from the #5 spot in 2021, this rise highlights a massive industry trend toward configuration-based vulnerabilities. Misconfigurations are rampant in cloud environments, containers, and API gateways, often stemming from default settings or a mistaken belief that cloud providers automatically handle security configurations.
-
SSRF Absorbed into Broken Access Control: Server-Side Request Forgery (SSRF) had its own spot in 2021 but has now been merged into A01: Broken Access Control. This makes sense practically: SSRF typically succeeds because an application fails to restrict which internal resources it is allowed to access, making it fundamentally an access control issue.
-
Classic Flaws Drop in Rank: Injection and Cryptographic Failures are still prevalent but carry less weight than before, dropping to #5 and #4 respectively. This decline indicates increased maturity in using modern frameworks and libraries, though these flaws still frequently appear in legacy code or custom implementations.
What This Means for Your Security Strategy
The overarching theme of the 2025 OWASP Top 10 is the need to look at the Software Development Life Cycle (SDLC) holistically. The most critical security risks today point to fundamental control issues: unclear trust in components, insufficient configuration management, and missing access controls.
To align with the 2025 recommendations, teams should prioritize the following:
-
Secure the Supply Chain: Treat supply chain risks as a core part of normal development. Generate and track Software Bill of Materials (SBOMs), utilize dependency scanning, and enforce integrity verification throughout your pipelines.
-
Automate and Verify Configurations: Manual configuration is a major liability. Configurations must be automated and continuously verified using Infrastructure as Code (IaC) scanning and security policies.
-
Design for Resilience: Cultivate a culture of “Security by Design” and “Security by Default.” Expect your systems to fail and ensure they handle errors securely. Access controls must be explicitly designed, documented, and tested.
Final Thoughts
Ultimately, the OWASP Top 10 2025 functions less as a warning list of new problems and more as a maturity mirror for your organization. By shifting your focus toward structure, clear ownership, and continuous lifecycle management, you can systematically defend against the systemic vulnerabilities that dominate today’s threat landscape.